Cyber Punk Vs. Leviathan Mac OS
Introduction
We already talked about Bettercap – MITM Attack Framework, but we decided to separate examples from the general tool info. Here, we’ll go over some Bettercap Usage Examples. There is a lot to cover, and things might not work as expected depending on the situation and network architecture, but we’ll try to cover as much as we can, updating this post as time goes by.
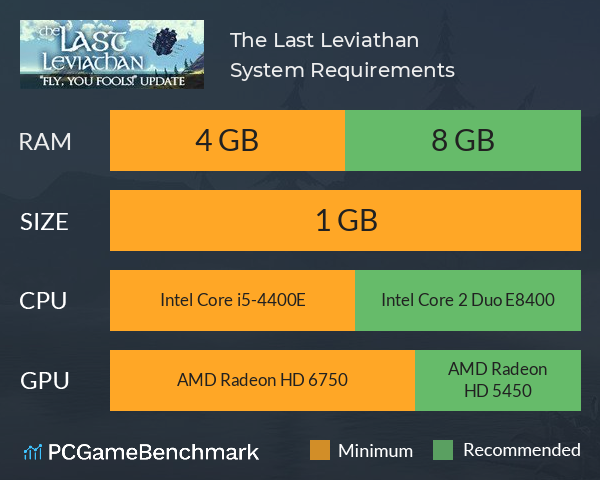
- The Sea Dragon Leviathan or more commonly known as Sea Dragon. Currently, it is the largest aggressive creature in Subnautica. It is a large, aquatic species that has adapted to volcanic environments. Although it’s body mostly resemble the Sea Emperor, the Sea Dragon Leviathan is smaller and is known for its dark green colored skin.
- Full range 2.0 gaming speakers for PC; Custom woven glass fiber 3-inch drivers for power and clarity; Rear-facing bass ports for powerful lows; Versatile controls for gaming, music and movies.
Jump to:
Transparent HTTP(S) Proxy
For HTTPS, enable http.proxy.sslstrip.We need to arp spoof victims address:
DLL files are small but exceptionally important files that apps on Windows 10 need to run. If these files are absent, or they’ve been corrupted, the app that needs them to run may become unstable, or it may not open at all.
Chrome will cause problems with HSTS preloaded sites, with message “Your connection is not private”. For non HSTS domains, it will allow you to proceed with “Proceed to <domain> (unsafe)” message. Internet Explorer will show similar message “There is a problem witt the website’s security ceritificate”. We’ll fight with HSTS (Hijacking) and SSL sites some other time.
DNS Spoofing
We need to define which domains we’re going to spoof, and to which ip to redirect them:
To spoof entire subnet, set:
Run it with:
You should probably also arp.spoof the subnet or the target.
ARP Spoofing
As before adjust the module:
All traffic from/to 192.168.1.6 will be redirected to you (bettercap). That’s going to cause connection issues on the target.
DNS/ARP Spoofing
One issue I experienced trying to spoof DNS/ARP are conflicts. By arp-ing the target and setting dns spoof, I was seeing nslookup returns conflicting data on the target side, as if my ARP poison and router argue with the target on who is right. I can clearly see address switching from second to second. Although on WiFi clients it seems to work, for targets on Ethernet (line):
and in the next second:
When I try to load the page, one moment it fails to load, in the next moment it’s fully loaded. One thing that manged to solve it permanently is to use:
» arp.ban on
Password Sniffing
For the purpose of example we’ll check some requests from the localhost. Start bettercap (maybe in –debug mode) and set:
You could setup an output file:
» set net.sniff.output ‘passwords.pcap’
so you can inspect packet dump later on with some tool like WireShark. Alternatively you can use some from the terminal:
By going to a domain and doing a couple of requests, we can see some captured traffic:
In the example above we have one form login and few GET password requests. GET requests are clearly visible inline. Form POST request visible in WireShark is also nicely formated within Bettercap:
You could use predefined caplet http-req-dump.cap:
Proxy JS Injection (XSS)
Within caplets repository we have beef-pasive.cap and beef-active.cap. I was unable to get any info with pasive one, but the active one works just fine. If we look at the caplet:
It sets the script, http proxy and it spoofs entire subnet. The beef-inject.js content:
It simply Logs the info in Bettercap console and injects the BeEF (The Browser Exploitation Framework Project) hook. Although BeEF is a great tool, you can also create your own script. Alter the line and set your own script instead of the hook.js (src=”http://<YOUR_SERVER>/my_hook.js”>). For e.g. set the content:
and run bettercap with eval (targeting specific computer in my LAN):
When user opens HTTP website, for instance time.com, hook will be executed and we’ll end up with:
XSS in the making.
Terminate Target Connectivity – Ban (LAN)
Start ARP spoofer in ban mode, meaning the target(s) connectivity will not work.
MAC Changer
Before you continue, check your current interface:
shut it down:
Then in bettercap, hit:
turn it on:
Now if you check ifconfig:
WiFi Network Monitoring (Playground)
New wifi.recon covers both 2.4 Ghz and 5Ghz frequencies. It’s doing everything you need. Deauth, Sniff, Handshake captures. To start, add -iface option:
Note: In case of an error: Can’t restore interface wlan0 wireless mode (SIOCSIWMODE failed: Bad file descriptor). Please adjust manually. Quit bettercap and manually set the wireless interface to monitor mode. For example, as follows:
Turn on recon:
You can manage channels with:
» wifi.recon.channel 10,11
To clear them:
» wifi.recon.channel clear
Results can be seen with:
To capture handshakes, we should define a sniffer, filter specific frames (0x888e), set the output file for processing later on, maybe select the channel and or target:
Then we should hit it with the Deauth. You can deauth all clients with:
or just specific one:
When you capture the handshake, you can start breaking them. We’ll not cover that here.
BLE (Bluetooth Low Energy device discovery)
The ble.recon will discovery every BLE device you want to inspect with ble.enum or playaround with ble.write.
To connect, enumerate and read characteristics from the BLE device 04:ff:de:ff:be:ff:
Write the bytes ff ff ff ff ff ff ff ff to the BLE device 04:ff:de:ff:be:ff on its characteristics with UUID 234afbd5e3b34536a3fe72f630d4278d:
Issues:
- ble.enum only works one time per execution
- incomplete support for macOS
- not supported on Windows
Caplets
Bettercap caplets, or .cap files are a powerful way to script bettercap’s interactive sessions, think about them as the .rc files of Metasploit. Check this repository for available caplets and modules. Some of them we already mentioned above, other we’ll leave for you to play with. From the names below you can see what’s already available:
- airodump.cap
- ap.cap
- ap-config.cap
- beef-active.cap
- beef-passive.cap
- crypto-miner.cap
- download-autopwn
- download-autopwn.cap
- fb-phish.cap
- gps.cap
- hstshijack
- http-req-dump.cap
- local-sniffer.cap
- login-man-abuse.cap
- massdeauth.cap
- mitm6.cap
- netmon.cap
- pita.cap
- proxy-script-test.cap
- recon-active.cap
- recon-passive.cap
- rest-api.cap
- rogue-mysql-server.cap
- rtfm.cap
- simple-passwords-sniffer.cap
- stsoy.cap
- tcp-req-dump.cap
- test-prompt-stats.cap
- web-override.cap
- wpa_handshake.cap
Conclusion
WiFi games, Redirection, Phishing, Sniffing, Injections, .. These Bettercap Usage Examples provide just a basic insight in how things work and what you can do, which is a lot (relatively). It can (and probably will) cause some headache while trying to do some specific attack, DNS issues, HSTS problems, SSLSplit issues, etc. Deal with it, explore. If nothing else, it will make you research things, understand how things work or don’t work. A tool you should maybe have in mind for some Pentesting, Neighbor exploring or cyberwarfare activities.
News
9 Mar 2016
Versions 4.1.0 and earlier of libotr in 64-bit builds contain an integer overflow security flaw. This flaw could potentially be exploited by a remote attacker to cause a heap buffer overflow and subsequently for arbitrary code to be executed on the user's machine.
CVE-2016-2851 has been assigned to this issue.
Please upgrade to libotr version 4.1.1 immediately.
Users of libotr packages in Linux and *BSD distributions should see updated packages shortly.
This security release includes the following updates:
- Fix an integer overflow bug that can cause a heap buffer overflow (and from there remote code execution) on 64-bit platforms
- Fix possible free() of an uninitialized pointer
- Be stricter about parsing v3 fragments
- Add a testsuite ('make check' to run it), but only on Linux for now, since it uses Linux-specific features such as epoll
- Fix a memory leak when reading a malformed instance tag file
- Protocol documentation clarifications
Cyber Punk Vs. Leviathan Mac Os Download
This point release includes the following updates:
- Fix use-after-free issue during SMP
- Updated Spanish, German, Norwegian Bokmål translations
- New Danish translation
- The Windows binary has been linked with updated versions of libotr, libgcrypt, libgpg-error, and other supporting libraries